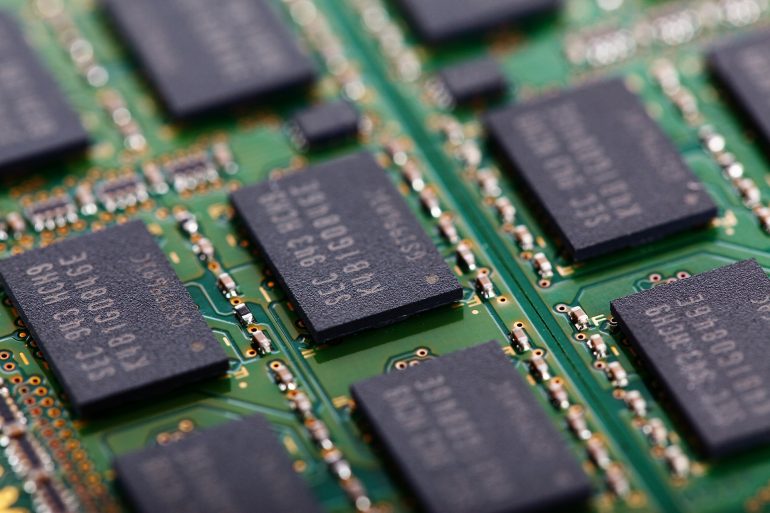
Data has become a valuable commodity. Many organisations collect vast amounts of sensitive data about their consumers as part of their core business model – some of this is used internally, while other data is sold to third parties as part of the organisation’s revenue model. Regardless of the type and purpose of the data collected, organisations need to be able to keep the data safe. Data protection is an important priority for any organisation, and many deploy data security solutions to help ensure that data is not inappropriately viewed or misused. However, new attack vectors have been created that can reduce or negate the effectiveness of organisations’ data security solutions. Chip vulnerabilities like Spectre leak data at a level not visible to software-based solutions. Other attack vectors like Rowhammer target how memory is stored in DRAM.
Based on the Rowhammer attack, a new vulnerability called RAMBleed has recently been discovered. Unlike Rowhammer, RAMBleed reads sensitive data from memory instead of blindly modifying it, making it a significant threat to organisational data security.
What is RAMBleed?
RAMBleed is an attack designed to use properties of DRAM to read data from memory locations not under the control of the attacker. The design of RAMBleed means that traditional process memory isolation does not protect the target memory.
The RAMBleed vulnerability is based upon the Rowhammer attack. Unlike RAMBleed, Rowhammer is designed to change the values of memory that the attacker does not control. As DRAM becomes more compact, the potential for adjacent memory cells to affect one another grows. Each bit in DRAM is stored as an electrical charge, meaning that the charge (and therefore the value of the bit) may flip based upon changes in the charge of adjacent bits. Rowhammer takes advantage of this by repeatedly flipping (hammering) the value of bits in rows above and below the target bit. This enables the attacker to flip the target bit, destroying the integrity of the target data.
One of the important principles of Rowhammer is that the target bit is more likely to flip if its value differs from the bits located directly above and below it. RAMBleed takes advantage of this to read the values of sensitive data. Using memory massaging techniques, the RAMBleed attack places a row of attacker-controlled memory between two rows of victim-controlled data. Then, the attacker performs a Rowhammer attack on their own memory and watches to see if it will flip. If it flips easily, the resulting value is probably the value of the victim’s data. Using this method, the researchers who discovered RAMBleed created a demo where they could read sensitive data like OpenSSH secret keys.
The effectiveness of the RAMBleed attack depends on two things: the ability of the attacker to organise memory on the target device and their ability to perform the Rowhammer attack. For their proof of concept, the researchers devised a way to abuse multiple aspects of the Linux system to organise memory the way that they wanted. Researchers around the world have also expanded the Rowhammer attack, demonstrating that it can be effectively applied and exploited in a variety of contexts. This means that the RAMBleed vulnerability is a significant threat to organisational data security.
Impacts of RAMBleed
RAMBleed is mainly a threat to data confidentiality in multi-tenant environments. The RAMBleed attack allows an attacker to read data adjacent to memory already under their control. If they have control over the target memory, then they don’t need the attack, so the attack is most dangerous in environments where a user has access to some memory and not that adjacent to it.
One example of a multitenant environment where RAMBleed can be a significant threat to data security is in cloud computing. Many cloud deployments are on multi-tenant cloud servers, meaning that the server’s memory and resources are shared among multiple customers. Under these circumstances, a malicious cloud user may use the RAMBleed vulnerability to read data from processes using memory adjacent to it. Since organisations are increasingly using the cloud for core business purposes and sensitive data processing, this vulnerability could have a significant negative impact on an organisation’s data security.
But RAMBleed isn’t only an effective attack vector against cloud computing. Malicious processes within a computer’s memory space can also use RAMBleed to read data from other processes on the machine. Many computers isolate process memory, but RAMBleed bypasses these protections. As a result, the combination of Rowhammer and RAMBleed means that malware can both modify and read memory of processes using adjacent memory spaces.
Securing Your Data
The RAMBleed vulnerability poses a significant threat to enterprise data security. If an attacker can run a malicious process on a vulnerable target machine and manipulate the memory space of the machine to place their memory segments next to memory segments of interest, they can extract the data in these segments. Running a malicious process on a target machine is nothing new (it’s the definition of malware), and the researchers have demonstrated the ability to manipulate a computer’s memory space, making this a viable attack vector.
Many users of multi-tenant cloud services rely on software-level isolation for privacy protection; however, RAMBleed bypasses these protections. To protect themselves, organisations need to deploy an enterprise-scale data protection solution that ensures that all sensitive data is stored in an encrypted form and that encryption keys are properly protected in a location immune to these attacks. This minimises the probability of a successful attack using RAMBleed since data is protected whenever possible.